Verify identity, prevent fraud, and improve access to your services with our solutions

Identity verification
Verify your clients, prevent fraud, and comply with requirements.
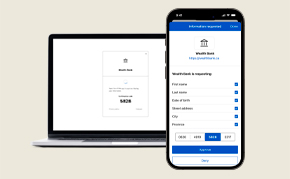
Digital ID / digital wallet
Store verified ID information on a secure digital wallet mobile app.

mDL mobile driver's licence
Provide a secure and compliant mobile driving licence.
eID-Me is perfect for these industries:
and other ID-enabled services
Join thousands of Canadian organizations that trust Bluink




